Cisco Talos researchers have documented phishing campaigns active since at least October 2025 that abuse n8n’s cloud automation webhooks to deliver malware and harvest victim data. By March 2026, the volume of phishing emails using these URLs had grown roughly eight times compared to January 2025.
n8n is the workflow automation platform we’ve mentioned several times recently for critical vulnerabilities in self-hosted instances. This is a different problem, and in some ways more insidious: there’s no bug to patch, no security update to deploy.
How the Attack Works
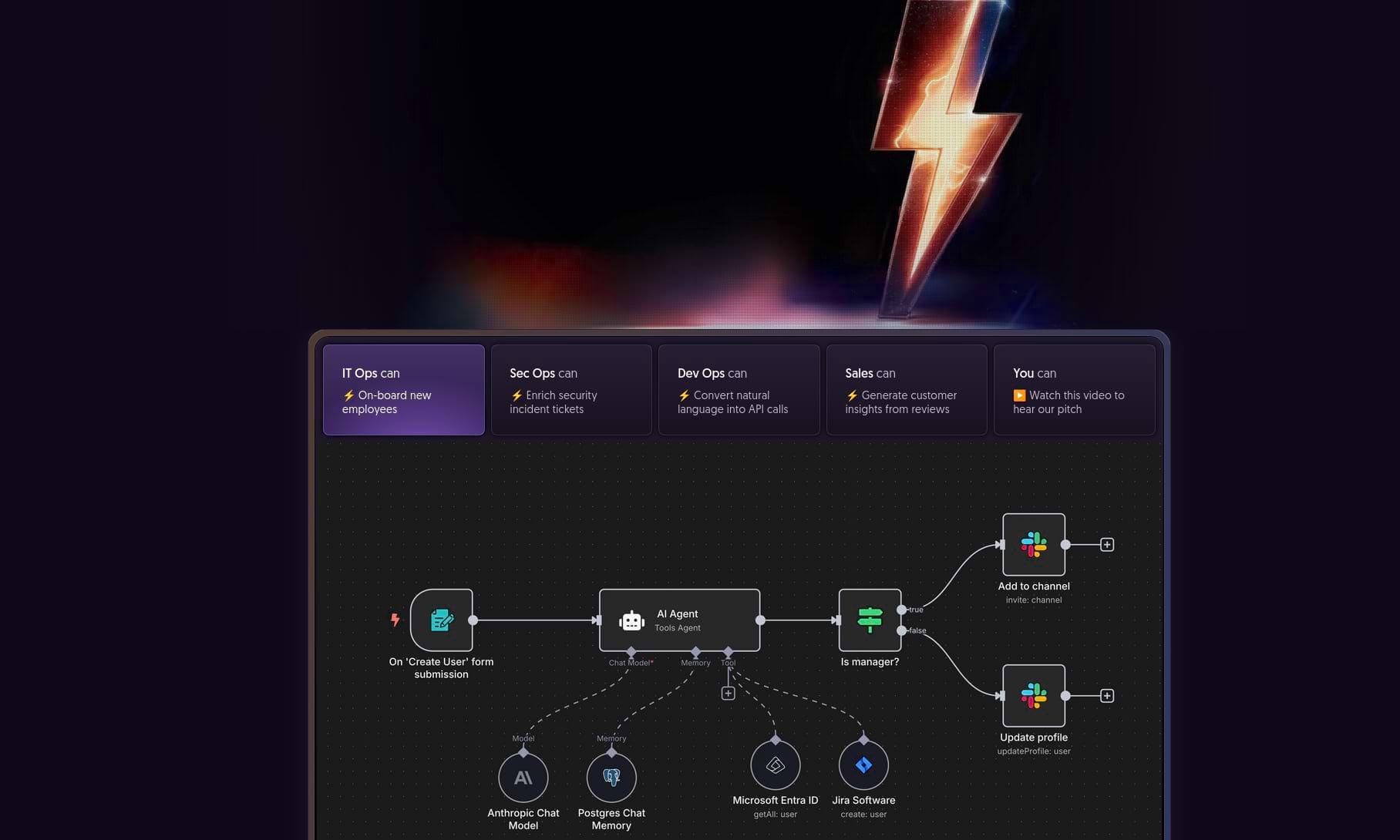
Anyone can open a free n8n cloud account and create workflows with webhook nodes, generating publicly accessible URLs in the format name.app.n8n.cloud/webhook/xxx. Each HTTP request to that URL triggers the workflow and returns a response. Attackers leverage this to build attack infrastructure operating under a domain that email filters and antimalware systems already trust.
Talos describes two primary variants. In the first, the phishing email contains a link to an n8n webhook displaying a fake CAPTCHA page. Once completed, a malicious executable downloads. Because the entire process occurs through n8n’s domain, the browser shows no warning flags. The final payload, according to Talos, is a modified version of legitimate remote management tools, used to establish persistent contact with a command-and-control server.
The Invisible Pixel
The second variant is less visible but equally effective. The email embeds an invisible image whose URL is an n8n webhook. When the email opens, the mail client automatically sends a GET request to that URL with parameters like the victim’s email address. The attacker gets a list of who opened the email, when, and with which client.
The Structural Problem
What makes this technique difficult to stop is exactly why it works: n8n is a legitimate service, used by developers and technical teams worldwide. The domain app.n8n.cloud isn’t suspicious by definition, and blocklisting it would interfere with entirely lawful workflows.
This isn’t the first time automation services have been weaponized this way. Similar campaigns have previously abused links on Dropbox, Google Docs, and other widely-trusted cloud tools. The logic remains constant: the more established and trustworthy a service is, the more useful it becomes as cover.

 Mastodon
Mastodon
 Telegram
Telegram
 Bluesky
Bluesky