When cPanel released its security bulletin on April 28, attacks were already underway for at least two months. KnownHost’s CEO confirmed this after finding the first exploitation attempts in their logs dating back to February 23. The vulnerability, now tracked as CVE-2026-41940 with a severity score of 9.8 out of 10, affects all supported versions of cPanel and WHM, the control panel managing tens of millions of websites worldwide.
How it worked
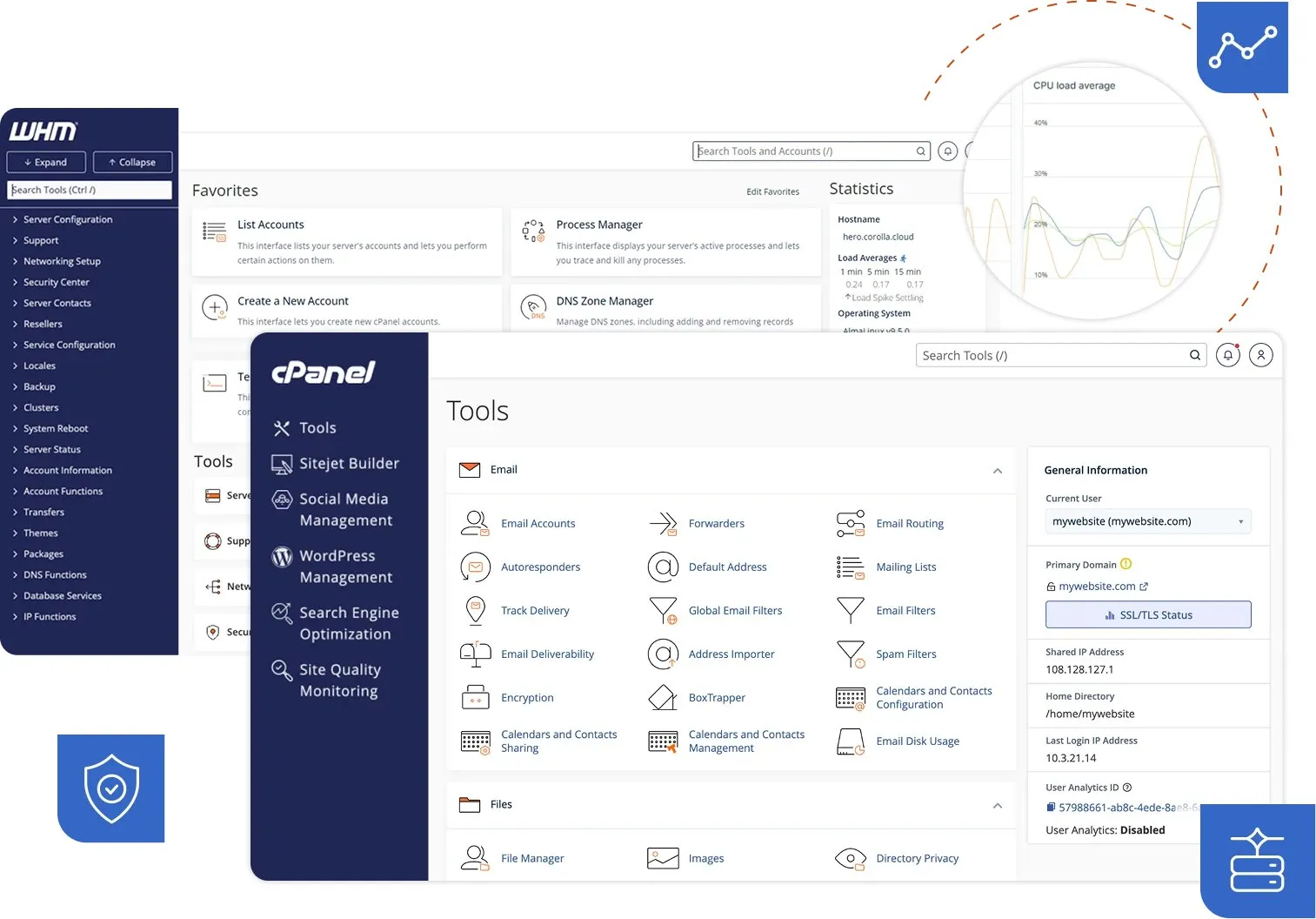
The mechanics were deceptively simple. cPanel writes a session file to disk for every login attempt, before even verifying credentials. The flaw was right there: by manipulating a session cookie with special characters, attackers could inject an arbitrary property into the session file, like user=root. When the session loaded next time, the system found an authentication marker already in place, skipped the password check, and granted full admin access. No credentials needed.
With roughly 1.5 million cPanel instances exposed on the internet, the potential blast radius is enormous. This isn’t just about the site owner’s server: on a shared hosting environment, a single compromised server can pull down hundreds of customer sites with it.
What to do now
If you’re on shared hosting, you likely can’t easily discover which cPanel version your provider is running. The most practical approach is to look for communications from your host about updates, or contact support directly asking whether CVE-2026-41940 has been patched. Providers like Namecheap and Hostgator have already publicly confirmed they’ve updated their systems.
If you manage a VPS or dedicated server with cPanel, checking is straightforward: the current version appears at the top of your WHM panel. The patched versions released on April 28 are: 11.110.0.97, 11.118.0.63, 11.126.0.54, 11.132.0.29, 11.134.0.20, and 11.136.0.5. To update via command line, run /scripts/upcp --force. If you’re using WP Squared, the WordPress hosting panel built on cPanel, upgrade to version 136.1.7.
As a temporary measure while waiting for updates, blocking inbound traffic on ports 2083, 2087, 2095, and 2096 reduces exposure. cPanel has also released a detection script for those wanting to check whether their session files already show signs of unauthorized access.
The U.S. CISA added CVE-2026-41940 to its list of actively exploited vulnerabilities, requiring U.S. federal agencies to apply the patch by May 3.

 Mastodon
Mastodon
 Telegram
Telegram
 Bluesky
Bluesky